Every line of custom code you write is a line that can be slow, misconfigurated, or exploited. That sounds like an argument against writing software at all, but it is actually the strongest argument for a different approach to building it. According to Veracode’s 2025 State of Software Security report, the average time to fix a security flaw has reached 252 days, up 47% since 2020, and half of all organizations carry critical security debt. The more custom code a codebase contains, the more attack surface exists, and the longer that surface takes to harden. This article explains precisely why less code, delivered through AI-powered no-code and low-code platforms, produces faster and more secure applications, and where that advantage is real versus where it has genuine limits. For context on how the broader platform landscape handles this trade-off, the comparison of no-code vs low-code for startups is a useful starting point.
TL;DR: Less custom code directly reduces attack surface, shortens development cycles, and pushes security responsibility to platform providers whose entire business depends on getting it right. According to Gartner, low-code development accounted for more than 70% of application development activity in 2025, up from 20% in 2020 (Gartner / CIO, 2025). The security and speed advantages are real, but only on platforms that have made security a default rather than an option.
Why Does More Code Create More Risk?
More custom code creates more risk because every unique line is a unique opportunity for error, misconfiguration, or exploitation. The relationship is not linear: it compounds. According to Black Duck’s 2025 Open Source Security and Risk Analysis report, 97% of commercial codebases contain open-source components, and 81% of those codebases have at least one high- or critical-risk open-source vulnerability. The problem is not just the code you write. It is the dependency chain of code you inherit.
Launch Your App Today
Ready to launch? Skip the tech stress. Describe, Build, Launch in three simple steps.
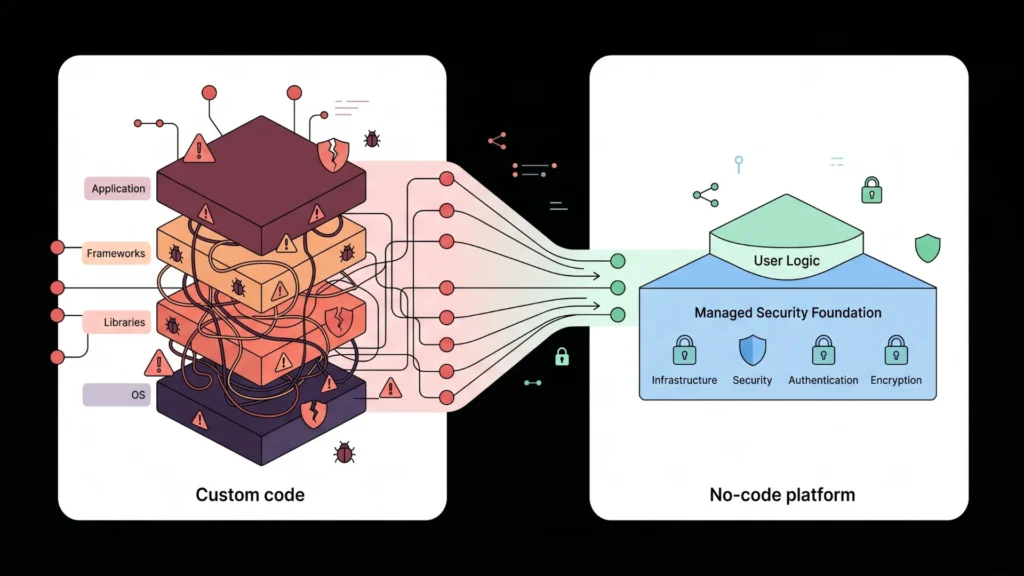
BuildTraditional software development stacks vulnerabilities in layers. A developer writes application logic on top of a framework, which runs on a runtime, which depends on dozens of libraries, which sit on an operating system, each with its own patch cycle and its own CVE history. In 2025, the National Vulnerability Database recorded a record 48,185 new CVEs, roughly 131 per day (NVD, 2025). Managing that exposure across a fully custom codebase requires constant vigilance, a security team, and a maintenance budget that most startups and small teams simply do not have.
No-code and low-code platforms change this equation by moving the majority of the stack to a managed layer the platform provider maintains and continuously hardens. Your custom logic sits on top. The infrastructure, authentication, encryption, and deployment are handled below. The result is a dramatically smaller surface of unique code that needs individual attention. The no-code tech stack guide for founders in 2026 explains how this layered model works in practice across the full build cycle.
The attack surface argument is the one most discussions miss. People frame no-code as “faster but less secure” when the opposite is frequently true for teams without dedicated security engineers. A custom-coded app built by a two-person startup carries every security burden in-house: dependency management, authentication implementation, session handling, encryption, access control. A no-code app on a production-grade platform offloads most of that to the provider. The startup’s job is to configure correctly and apply role permissions thoughtfully. That is a security model that matches the actual resources available to most product teams.
Citation capsule: According to Veracode’s 2025 security maturity benchmarks, leading organizations fix half of all security flaws within 5 weeks, while lagging organizations take over a year. The primary driver of that gap is the volume of custom code requiring individual attention. Organizations that reduce their custom codebase through managed platforms shrink the patch backlog structurally rather than operationally (Veracode, 2025).
How Does Less Code Accelerate Development Speed?
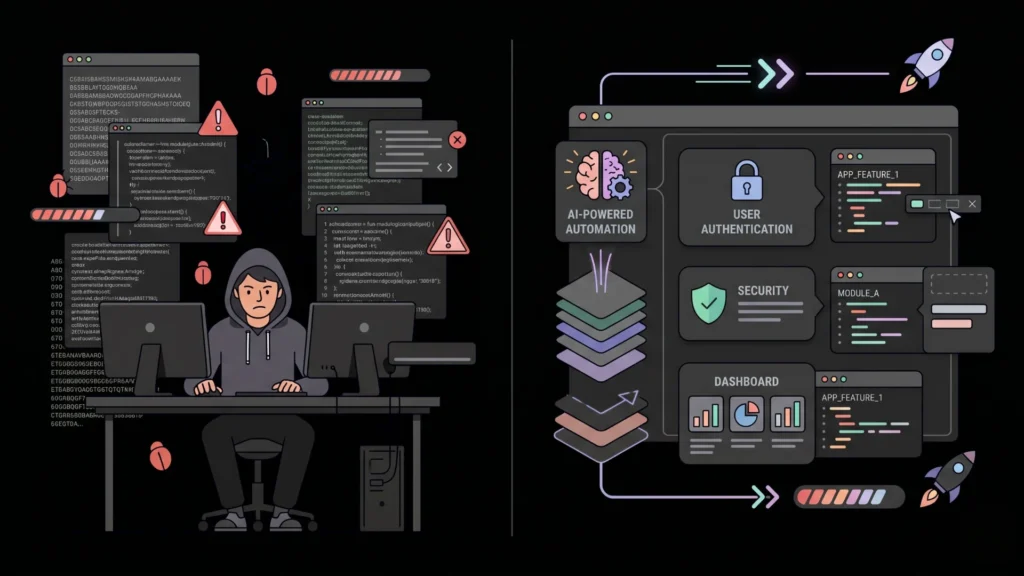
Less code speeds development in two distinct ways: it removes the time spent writing code that already exists as a maintained abstraction, and it removes the time spent debugging, testing, and securing that code after the fact. Both effects are significant, and they compound over the lifetime of a product. According to Gartner, organizations adopting low-code platforms report development cycles 50 to 70% faster compared to traditional methods (Gartner, 2026).
The first effect is obvious. When you describe an authentication system in plain English and an AI-powered platform generates the full implementation, including secure session management, password hashing, and email verification, you skip weeks of work that would otherwise go to writing, testing, and securing that infrastructure. That is time redirected to the actual product logic that differentiates your application.
The second effect is less discussed but equally important. Traditional development teams spend between 30 and 50% of their time fixing bugs and dealing with unplanned rework, according to the Consortium for Information and Software Quality (CISQ, 2025). Bugs found in production are dramatically more expensive and time-consuming to fix than those caught at design time, because by production, a defect has been integrated into multiple systems, shipped to users, and compounded by downstream effects. Platforms that generate tested, standardized components eliminate entire categories of implementation bugs before they can enter the codebase. You cannot introduce a SQL injection vulnerability in code you did not write.
The speed benefit is also structural, not just one-time. Custom codebases grow in complexity as features are added, and complexity increases the time required for every subsequent change. Managed platform code stays stable in its core functionality while your custom layer grows on top. That separation keeps your iteration velocity high even as the product matures.
Citation capsule: According to a 2024 Gartner report cited by American Chase (2025), businesses using low-code and no-code platforms delivered MVPs 50 to 70% faster with an average cost reduction of 50 to 65% compared to traditional development. Development teams using managed platforms also avoid the 30 to 50% of development time typically consumed by bug fixing and unplanned rework, according to CISQ’s 2025 analysis of poor software quality costs (Gartner / CISQ, 2025).
What Security Defaults Does a Production-Grade No-Code Platform Provide?
Security defaults are the foundation of the less-code security advantage. They only deliver real protection when the platform has implemented them correctly and made them non-optional. The distinction between a platform that offers security features and one that enforces them by default is the difference between a tool and a safety net. OutSystems’ 2025 low-code security analysis notes that quality platforms provide built-in authentication methods, standardized encryption implementation, automated session management, and pre-configured templates that reduce misconfigurations (OutSystems, 2025).
On imagine.bo, every application deployed through the platform ships with a specific set of security defaults that require no additional configuration from the builder:
SSL and HTTPS on all deployments. Every application gets encrypted transport by default. There is no opt-in required and no risk of accidentally shipping an unencrypted endpoint because a developer forgot to configure a certificate.
Data encryption at rest and in transit. The database and API communications are encrypted at the platform level. Builders do not manage encryption keys or cipher selection.
Role-Based Access Control at the data layer. RBAC on imagine.bo is enforced at the database layer, not just the user interface. This is the distinction that matters. A UI-only access control can be bypassed by a direct API call. A data-layer RBAC cannot be. Specifying user roles explicitly in the Describe-to-Build prompt produces a generated system where those permissions are structurally enforced.
GDPR and SOC2 readiness foundations. Compliance architecture is baked into deployment by default. The GDPR compliance guide for no-code tools explains what this covers and where additional implementation is required for full certification.
Vercel and Railway infrastructure. Frontend deployment on Vercel delivers global edge caching, DDoS mitigation, and automatic HTTPS. Backend deployment on Railway handles autoscaling, isolated runtime environments, and production-grade uptime. Both are maintained by providers whose security posture is their product.
The most common security gap in no-code apps is not a platform failure. It is a configuration error at the role definition layer. A builder who prompts for an admin dashboard without explicitly specifying that only admin-role users can access it may generate a dashboard with UI-level restrictions but no backend enforcement. Specifying role constraints explicitly in the initial Describe-to-Build prompt, including what each role can read, write, edit, and delete, is the single most important security action a no-code builder can take. The prompt-based app security best practices guide covers the exact prompting patterns that produce correctly enforced access control from the first generation pass.
Citation capsule: According to OutSystems’ 2025 low-code security analysis, well-designed low-code platforms reduce attack surface by using controlled development environments, pre-vetted components, automated security checks, and standardized configurations that lower the risk of misconfigurations becoming breaches. The security model shifts responsibility from individual developers to the platform provider, which is a net security improvement for teams without dedicated security engineers (OutSystems, 2025).
Where Are the Real Security Limits of Less Code?
Honesty about the limits is what separates this from marketing copy. Less code on a no-code platform does not eliminate all security risk. It changes the risk profile. The residual risks are real and worth understanding before you build anything handling sensitive data.
Configuration errors by the builder remain possible. A CIO.com analysis (2025) correctly notes that if builders create apps faster than they can be secured, they build dangerous blind spots. The platform handles infrastructure security. The builder handles access control logic, data field exposure, and integration permissions. Getting those wrong is still possible, and the speed advantage of no-code means those errors can be shipped to production faster if builders do not review what they have built.
Platform-level vulnerabilities exist. When a significant security flaw exists in the platform infrastructure, every application on that platform is exposed until the provider patches it. This is the trade-off of using a shared managed platform: your security posture is partially dependent on the provider’s response time. Choosing a provider with a documented security track record, a clear CVE disclosure policy, and regular penetration testing is the mitigation.
Third-party integrations require engineering oversight. Payment gateways, external APIs, and data-sharing integrations introduce compliance and security complexity that no-code generation handles imperfectly. This is precisely the use case for imagine.bo’s Hire a Human feature: payment integrations, health data connections, and authentication flows that touch regulated data benefit from the review of a vetted engineer who understands the compliance requirements. Why Hire a Human matters when AI reaches its limits explains the model and when to trigger it.
AI-generated code is not immune to bugs. Cycode’s 2026 State of Product Security report found that AI-generated code has become the number-one blind spot for application security teams, with over 92% of organizations using AI coding assistants while lacking adequate review of the output (Cycode, 2026). The same applies to AI-generated no-code applications. Reviewing the AI-Generated Blueprint before deployment is not optional. It is the step that keeps the speed advantage from becoming a security liability.
Citation capsule: According to Cycode’s 2026 State of Product Security in the AI Era report, over 92% of organizations are actively using or piloting AI coding assistants, yet AI-generated code has become the number one blind spot for application security teams. In the first half of 2025, the National Vulnerability Database coordinated over 23,667 CVEs, an increase of 16% from the prior year, reflecting a security landscape where speed of deployment and speed of vulnerability emergence are rising in parallel (Cycode / NVD, 2026).
How Does Less Code Affect Application Performance Speed?
Security and development speed are two of the three ways less code improves modern apps. The third is runtime performance, which operates through a different mechanism but connects to the same principle: managed infrastructure maintained at scale performs better than custom infrastructure maintained by a small team.
imagine.bo’s One-Click Deployment pushes frontend code to Vercel. Vercel’s global edge network caches and serves content from the point of presence closest to each user, delivering load times that would require significant DevOps investment to replicate on a self-managed server. The backend runs on Railway, which handles autoscaling automatically. When your application goes from 10 concurrent users to 1,000, the infrastructure responds without manual intervention or downtime.
For builders who want to understand how the architecture decisions that produce this performance profile fit together, the scalable SaaS architecture for no-code platforms breaks down the underlying model in detail. The short version: edge CDN delivery, serverless-compatible backend architecture, and managed database infrastructure produce performance characteristics that most small teams cannot reproduce with a custom stack.
Based on imagine.bo’s deployment model, a production application deployed through the platform benefits from Vercel’s global edge network, which Vercel reports as serving more than 100,000 deployment events per day across its infrastructure. The same application self-deployed on a single cloud VM by a team without DevOps expertise would require significant additional configuration to approach the same geographic distribution, automatic failover, and cache optimization. The platform’s managed infrastructure represents years of accumulated performance engineering that no individual team replicates from scratch.
Citation capsule: According to Gartner (2026), by 2026, 75% of new applications will include components built with low-code or no-code platforms, with AI-powered low-code expected to enable up to 80% of business app development by 2029. The performance infrastructure underlying production no-code platforms, including edge CDN delivery, autoscaling backends, and managed SSL, represents enterprise-grade capability delivered at consumer pricing (Gartner, 2026).
FAQ
Does less code actually mean fewer security vulnerabilities in production?
For teams without dedicated security engineers, yes. Production-grade no-code platforms handle authentication, encryption, session management, and access control through maintained, tested implementations. According to OutSystems (2025), well-designed platforms reduce attack surface through pre-vetted components and standardized configurations. The residual risk is configuration error by the builder, not implementation error in platform infrastructure. The prompt-based app security best practices guide covers how to minimize that residual risk at the prompt-writing stage.
How much faster is no-code development compared to traditional coding?
Gartner data cited by American Chase (2025) puts the range at 50 to 70% faster delivery with 50 to 65% lower cost. For MVP-grade applications, the difference is often measured in days vs. months. A standard SaaS MVP with authentication, user roles, and core workflows takes one to three days on imagine.bo versus three to six months and $55,000 to $140,000 via traditional development. The speed comes from eliminating the implementation of infrastructure that already exists as a maintained abstraction.
What is the biggest security risk with no-code apps?
Misconfigured access control, not platform-level vulnerabilities. Builders who do not explicitly define which user roles can access which data may generate apps with UI-level restrictions that lack backend enforcement. On imagine.bo, RBAC is implemented at the data layer, but it must be correctly specified in the Describe-to-Build prompt. The 10 critical mistakes to avoid when building a no-code app covers access control errors and the other common failure points in detail.
Can a no-code app be GDPR or SOC2 compliant?
It can meet the foundational requirements. imagine.bo ships every application with GDPR and SOC2 readiness foundations: SSL/HTTPS, data encryption, RBAC, and structured data ownership. Full certification for regulated use cases requires additional controls and in some cases specialized engineering. The Hire a Human feature connects you with engineers who can implement those controls without leaving the platform workflow. According to Netguru (2026), organizations on modern platforms see 40 to 60% fewer compliance violations than those on legacy systems.
Is AI-generated code more or less secure than human-written code?
Neither is inherently more secure. Both are susceptible to logic errors and misconfiguration. What AI-generated code on a managed platform does differently is eliminate entire categories of implementation error by reusing proven, tested components for standard functions like authentication and encryption. The risk, as Cycode’s 2026 report identifies, is that AI-generated code is reviewed less carefully because speed encourages shipping without thorough review. Treating the AI-Generated Blueprint as something to audit, not just accept, is the discipline that captures the speed benefit without the security downside. The AI-driven cybersecurity automation guide for no-code explores how automation and security intersect across the no-code stack.
Conclusion
Three things are worth carrying forward. First, the security and speed advantages of less code come from the same source: platform providers absorb the complexity and maintenance burden that individual teams cannot scale to match. For a two-person startup, writing custom authentication is not a security-first decision. It is a liability. Using a platform whose entire business depends on authentication working correctly is a better bet. Second, the residual risk is real and specific: access control configuration, third-party integration oversight, and reviewing what the AI generated before deployment. None of those require engineering expertise. They require careful thinking about who can see what, and the discipline to check the blueprint before you ship. Third, performance is not a separate benefit. Edge infrastructure, autoscaling, and managed SSL are part of what you get when you trade custom code for a managed platform. That trade improves security, speed, and runtime performance simultaneously, not one at a time.
If you are building something today and weighing this trade-off, start with the build an AI app people buy and keep playbook to understand how these principles translate into actual product decisions. Then describe your application in plain English on imagine.bo’s Pro plan, review the AI-Generated Blueprint with fresh eyes, define your user roles explicitly, and deploy with One-Click Deployment to Vercel and Railway. The security and performance infrastructure is already there. Your job is to configure the layer that sits on top of it correctly.
Launch Your App Today
Ready to launch? Skip the tech stress. Describe, Build, Launch in three simple steps.
Build