A failed payment is not just a technical glitch. It is a customer you lose before they finish buying and revenue that does not come back. According to Stripe’s own published data, card declines and payment errors account for billions of dollars in lost revenue for businesses annually, with a significant share of those failures caused by fixable implementation and configuration issues rather than genuine customer inability to pay (Stripe, 2024). If you are running a SaaS, ecommerce store, or any web application that processes payments, understanding why Stripe errors happen and how to resolve them quickly is a direct revenue competency. This guide covers the five most common Stripe payment errors, exactly what causes each one, and the specific steps to fix them. For a broader view of payment integration challenges in no-code and AI-built apps, this post on common Stripe payment integration challenges explained is a useful companion.
TL;DR The five most common Stripe errors are card declines, webhook failures, authentication errors, API key misconfigurations, and currency or region mismatches. Most are fixable in under an hour with the right diagnostic approach. According to Baymard Institute, 70.19% of shopping carts are abandoned on average, and payment errors that occur at checkout make that number significantly worse (Baymard Institute, 2024). Each error type has a distinct cause and a distinct fix. Treating them all as the same problem is the most common reason they persist.
Why Do Stripe Payment Errors Happen So Often?
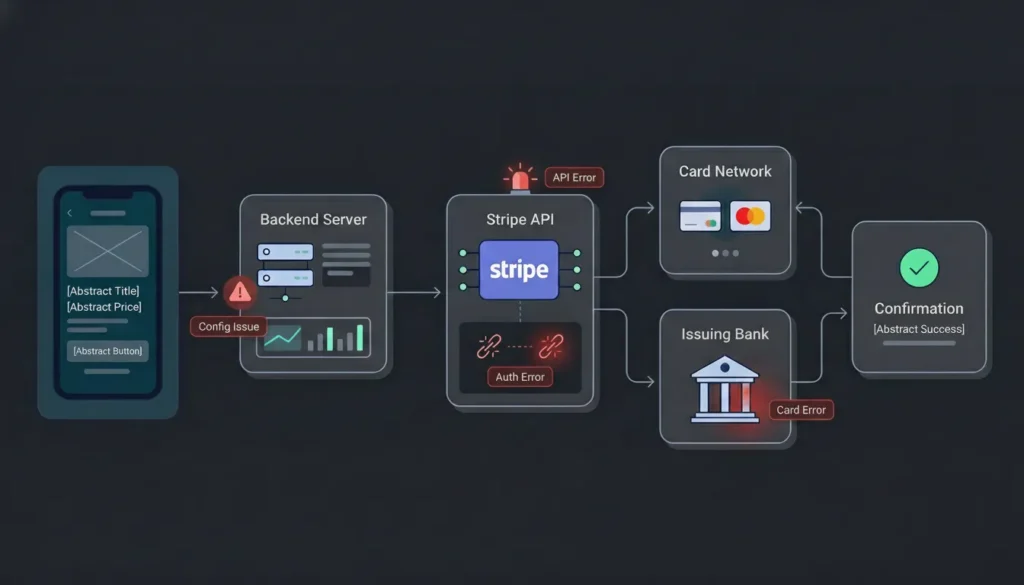
Stripe payment errors happen so often because payment processing involves more moving parts than most developers and founders expect. A single transaction passes through your frontend, your backend, the Stripe API, the card network, the issuing bank, and back again, and any point in that chain can fail for different reasons. According to Stripe’s developer documentation, there are over 30 distinct error codes in their API, grouped into categories including card errors, API errors, idempotency errors, and authentication errors (Stripe, 2024).
Launch Your App Today
Ready to launch? Skip the tech stress. Describe, Build, Launch in three simple steps.
BuildThe errors that hurt businesses most are not always the most technically complex. A misconfigured API key in production, a webhook endpoint that is not handling HTTPS correctly, or a card charge attempt using the wrong currency code are all simple configuration failures that stop real revenue cold. Knowing which error category you are dealing with before you start debugging saves hours. This overview of payment gateway integration in no-code apps covers the full integration architecture that Stripe errors typically occur within.
Error 1: Card Declined (card_declined)
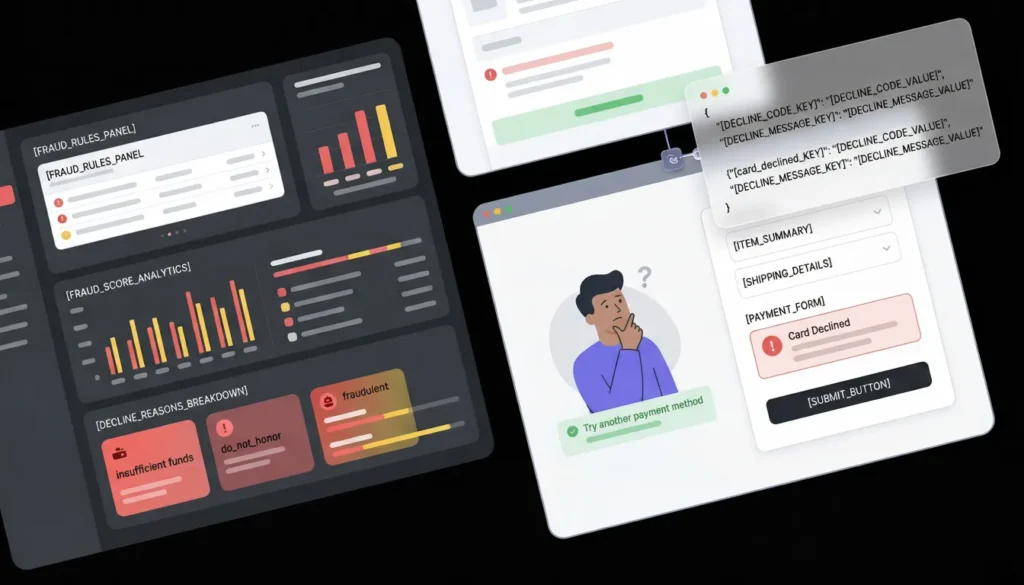
Card decline errors are the most common Stripe error type by volume, and they are also the most frequently misdiagnosed. A card_declined error from Stripe does not mean the card is invalid. It means the issuing bank rejected the charge, and the reason varies significantly by the decline code attached to the response. According to Stripe, the most common decline sub-reasons include insufficient funds, the generic do_not_honor code from the issuing bank, and suspected fraud triggers (Stripe, 2024).
What the error looks like:
{
"error": {
"code": "card_declined",
"decline_code": "insufficient_funds",
"message": "Your card has insufficient funds.",
"type": "card_error"
}
}The decline_code field is where the real diagnostic information lives. insufficient_funds is customer-facing and unfixable on your end. do_not_honor is a generic bank refusal that often means the card issuer flagged the transaction as unusual. fraudulent is Stripe’s own fraud prevention system triggering, not the issuing bank.
How to fix it by decline code:
For insufficient_funds and do_not_honor: these are genuine issuer-side declines. The fix is customer communication, not code changes. Surface a clear, specific error message that tells the customer to try a different card or contact their bank. A generic “payment failed” message at this point loses customers who would have completed the purchase with better guidance.
For fraudulent or Stripe Radar blocks: review your Radar rules in the Stripe Dashboard under Radar > Rules. If legitimate customers are being flagged, your risk rules may be too aggressive for your customer profile. Common over-triggers include customers checking out from VPN exit nodes, international cards on a domestic store, or first-time purchases above a threshold that matches your fraud rule settings. Adjust the threshold or add an allowlist rule for your known-good customer segment.
For card_not_supported: the card type does not support the charge type you are attempting. If you are processing recurring charges, confirm the card supports subscriptions. Some prepaid and debit cards do not.
The single most effective change for reducing declined card abandonment is adding a Stripe Payment Element rather than a custom card form. The Payment Element automatically surfaces the payment methods most likely to succeed for a given customer’s location and device, and Stripe’s Link feature lets returning customers pay in two clicks. Merchants who switch from custom card forms to the Payment Element consistently see conversion rate improvements because the element handles card validation and formatting client-side before the charge attempt reaches the API.
Citation capsule: According to Stripe, businesses using Stripe’s optimized checkout surfaces see conversion rates up to 10.5% higher than those using custom-built payment forms, because Stripe’s machine learning optimizes payment method presentation per customer in real time (Stripe, 2024).
For broader context on how to handle payment integration in no-code and AI-built applications, this post on Stripe payment processing errors and resolutions covers the implementation patterns in more detail.
Error 2: Webhook Delivery Failures
Webhook failures are the silent killer of Stripe integrations. Unlike card declines that surface immediately to the customer, a failing webhook produces no visible error in your app. The payment succeeds, but the downstream business logic never fires: the subscription does not activate, the order does not fulfill, the user account does not upgrade. According to Stripe’s developer documentation, webhook delivery failures are one of the most common causes of broken post-payment flows in production applications (Stripe, 2024).
What the error looks like:
In your Stripe Dashboard under Developers > Webhooks, failed delivery attempts appear with HTTP status codes. The most common failure responses are:
400 Bad Request: your endpoint received the webhook but returned an error, usually because your handler threw an exception401 Unauthorizedor403 Forbidden: your endpoint rejected the request, often because signature verification failed404 Not Found: the webhook URL does not exist or the route is not registeredtimeout: your endpoint took longer than 30 seconds to respond, which Stripe treats as a failure
How to fix it:
Start with signature verification. Every Stripe webhook includes a Stripe-Signature header that you must verify using your webhook signing secret from the Dashboard. If you are not verifying this header, any request to your webhook endpoint, including malicious ones, will be processed. The verification code is straightforward:
javascript
const sig = request.headers['stripe-signature'];
let event;
try {
event = stripe.webhooks.constructEvent(
request.rawBody,
sig,
process.env.STRIPE_WEBHOOK_SECRET
);
} catch (err) {
return response.status(400).send(`Webhook Error: ${err.message}`);
}The most common reason this fails in no-code and AI-built apps is that the framework parses the request body as JSON before the signature check runs. Stripe requires the raw, unparsed body for signature verification. If your framework JSON-parses automatically, you need to configure a raw body parser specifically for the webhook route.
For timeout failures: your webhook handler must return a 200 response within 30 seconds. Any long-running business logic, such as sending emails, updating a database, or calling external APIs, should be queued and processed asynchronously. Acknowledge the webhook immediately and process the work in a background job.
For 404 failures: confirm your webhook URL is correctly registered in the Stripe Dashboard and that your production deployment has the route active. In imagine.bo-generated applications, use the Hire a Human feature for webhook implementation specifically, since correct signature verification and async processing require precise engineering rather than conversational prompt refinement.
A subscription SaaS charging $49 per month that fails to activate 5% of successful payments due to webhook failures loses approximately $2,940 per year on every 100 new subscribers. At 1,000 subscribers per year that is $29,400 in silent revenue leakage, entirely from a configuration error that takes under two hours to fix correctly.
Citation capsule: Stripe recommends handling webhooks idempotently by checking the event ID before processing, because Stripe may deliver the same webhook event more than once, and duplicate processing of a payment confirmation or subscription activation can cause double-fulfillment errors that are harder to debug than the original webhook failure (Stripe, 2024).
Error 3: Authentication and API Key Errors
Authentication errors stop payment processing entirely and are almost always configuration problems rather than code bugs. The two most common authentication errors in Stripe are using a test API key in production and using a secret key client-side where a publishable key is required. According to Stripe’s error documentation, invalid_api_key and authentication_required errors account for a disproportionate share of developer-reported integration issues during the first 30 days after a production launch (Stripe, 2024).
What the errors look like:
{
"error": {
"type": "invalid_request_error",
"message": "No such API key: 'sk_test_...'",
"code": "api_key_invalid"
}
}
{
"error": {
"type": "card_error",
"code": "authentication_required",
"message": "This card requires authentication."
}
}These are two completely different problems that share a naming proximity. api_key_invalid means your server is sending the wrong key. authentication_required means the card transaction requires 3D Secure authentication and your integration is not handling the redirect flow.
How to fix API key errors:
Stripe provides four keys: a test publishable key (pk_test_), a test secret key (sk_test_), a live publishable key (pk_live_), and a live secret key (sk_live_). The publishable key goes in your frontend JavaScript. The secret key goes in your server-side environment variables and must never be exposed in client-side code.
The most common misconfiguration in AI-generated and no-code applications is hardcoding keys in frontend components during development and forgetting to move them to environment variables before production deployment. Run this check before any production launch:
- Search your entire codebase for
sk_test_orsk_live_. If either string appears outside an environment variable definition, you have a security exposure. - Confirm that your production environment variables contain
sk_live_values, notsk_test_values. - Confirm that your frontend only references the publishable key, never the secret key.
How to fix authentication_required errors:
authentication_required means the card requires 3D Secure (3DS) verification. This is mandatory for many European cards under PSD2 regulation and increasingly common globally. Your integration must handle the requires_action status returned by the PaymentIntent API and redirect the customer through the 3DS flow before confirming the charge.
If your integration is using Stripe’s Payment Element or Checkout, this is handled automatically. If you built a custom payment flow, you need to implement the confirmation step that handles requires_action. This is a case where using imagine.bo’s Hire a Human feature for the 3DS implementation is the right call. Getting it wrong means European customers consistently fail at checkout with no visible error, because the authentication_required error only surfaces when the 3DS step is skipped entirely.
The authentication_required error is frequently misread as a card decline by founders who do not check the error code carefully. A customer who abandons checkout after seeing a generic error message because your integration skipped 3DS is counted as cart abandonment in your analytics, not as a payment error. This means the real cost of missing 3DS support is invisible in most standard analytics dashboards, and the actual conversion rate impact is consistently underestimated until the error is explicitly logged and tracked by code rather than payment outcome.
For security best practices around API key management and payment implementation in no-code applications, this post on prompt-based app security best practices covers the implementation patterns that prevent exposure.
Error 4: Idempotency and Duplicate Charge Errors
Idempotency errors are among the least understood Stripe errors and among the most expensive when they go unaddressed. An idempotency error occurs when a network timeout or a client retry causes the same payment request to be sent to Stripe more than once. Without idempotency keys, duplicate charges happen. With incorrectly reused idempotency keys, legitimate new payments fail. According to Stripe’s developer documentation, idempotency handling is one of the most commonly skipped steps in payment integration, particularly in applications built by non-specialist developers (Stripe, 2024).
What the error looks like:
{
"error": {
"type": "idempotency_error",
"message": "Keys for idempotent requests can only be used with the same parameters they were first used with.",
"code": "idempotency_key_in_use"
}
}This error occurs when you reuse an idempotency key with different request parameters, typically because you are generating idempotency keys incorrectly, using a static value per session rather than a unique value per payment attempt.
How to fix it:
Every Stripe API request that creates or modifies a resource should include an Idempotency-Key header. The key must be unique per payment attempt and consistent across retries of the same attempt. The standard pattern is to generate a UUID when the customer initiates checkout and attach it to every API call for that transaction:
javascript
const idempotencyKey = `pay_${userId}_${orderId}_${Date.now()}`;
const paymentIntent = await stripe.paymentIntents.create(
{
amount: 4900,
currency: 'usd',
customer: customerId,
},
{
idempotencyKey: idempotencyKey,
}
);Store the idempotency key with the pending order in your database. If a retry occurs because of a network timeout, send the same key. Stripe returns the original successful response rather than processing a second charge.
Duplicate charge incidents are the most damaging Stripe error type from a customer relationship perspective. A customer who sees two charges for the same purchase immediately disputes both, contacts their bank, and often leaves a negative review before you even know the duplicate happened. The fix is architectural, not reactive. Building idempotency key generation into your payment initiation flow from day one prevents this entirely. In imagine.bo-generated applications, include idempotency requirements explicitly in your payment integration prompt: “Generate a unique idempotency key per payment attempt and store it with the order record to prevent duplicate charges on retry.”
Citation capsule: Stripe processes millions of payment requests per day across its global network, and network timeouts that trigger client retries are a normal occurrence rather than an edge case. Stripe’s documentation explicitly classifies idempotency key usage as a required implementation pattern rather than an optional best practice, because the alternative is duplicate charges that cannot be automatically detected without explicit deduplication logic on the merchant side (Stripe, 2024).
For a full overview of common mistakes in no-code SaaS development including payment integration errors, this post on common mistakes in no-code SaaS development and how to avoid them covers the broader pattern.
Error 5: Currency and Region Mismatch Errors
Currency and region errors are the most common Stripe failure pattern for founders building products for international markets or for businesses operating in regions with specific payment requirements. These errors do not look like errors to the customer. The charge attempt simply fails silently or returns a decline that no amount of card-switching resolves. According to Stripe’s documentation, currency mismatch errors and unsupported payment method errors are among the top ten most-reported integration issues by developers building multi-currency or international applications (Stripe, 2024).
What the errors look like:
{
"error": {
"type": "invalid_request_error",
"message": "Currency 'inr' is not supported by this PaymentMethod.",
"code": "payment_method_currency_not_supported"
}
}
{
"error": {
"type": "invalid_request_error",
"message": "Amount must be at least $0.50 usd",
"code": "amount_too_small"
}
}How to fix currency mismatch errors:
Stripe requires that the currency in your PaymentIntent match the currency the customer’s payment method supports. Many Indian cards, for example, will not process USD charges without international transaction enablement. Many European payment methods require EUR. If your backend hard-codes currency: 'usd' for all transactions, you will silently fail every customer whose card does not support USD charges.
The fix is dynamic currency handling based on customer location:
javascript
const currencyMap = {
'IN': 'inr',
'EU': 'eur',
'GB': 'gbp',
'US': 'usd',
};
const currency = currencyMap[customerCountry] || 'usd';For the amount_too_small error: Stripe requires a minimum charge amount per currency. For USD this is $0.50, for INR it is ₹0.50, for JPY it is ¥50. Zero-decimal currencies like JPY do not use cents and require amounts passed without decimal conversion. A common bug is multiplying a JPY price by 100 the way you would for USD, resulting in a charge 100 times the intended amount.
How to fix region-specific payment method errors:
If your Stripe account is registered in one country and you are attempting to process payments in another, certain payment methods and currencies may not be available. India-registered Stripe accounts, for example, require compliance with RBI export regulations for international payments. The correct fix varies by region and account configuration, and this is the specific scenario where using imagine.bo’s Hire a Human feature is strongly recommended over attempting to resolve through prompt iteration alone. Payment compliance requirements are jurisdiction-specific and change. Engineering oversight from someone familiar with your regional Stripe configuration prevents compliance failures that are harder to fix than technical errors.
imagine.bo’s built-in security defaults include SSL on all deployments and RBAC for user roles. But payment compliance, specifically currency routing, webhook security, and regional payment method support, benefits from the Hire a Human workflow for precise implementation. These are not areas where approximate code generates acceptable outcomes. For a comprehensive overview of no-code app security patterns that apply to payment implementations, this post on no-code app security best practices covers the implementation layer in detail.
Citation capsule: Stripe supports over 135 currencies and 40 payment methods globally, but not every payment method is available in every country or for every Stripe account registration. According to Stripe’s documentation, the correct approach for multi-currency applications is to query the Payment Methods API dynamically based on the customer’s billing country rather than hard-coding currency values, because available payment methods change based on account capabilities, customer location, and regulatory requirements (Stripe, 2024).
How to Debug Stripe Errors Systematically
Every Stripe error contains a type, a code, and usually a decline_code or message field. Reading all three before taking any action eliminates the most common debugging mistake, which is treating all Stripe errors as the same category of problem.
A practical debugging sequence for any Stripe error:
- Check the
typefield first.card_errormeans the issuer rejected the charge.api_errormeans something is wrong with your integration or Stripe’s infrastructure.invalid_request_errormeans your request parameters are incorrect. - Check the
codefield second. This identifies the specific error category and maps to the Stripe documentation for that code. - Check the
decline_codefield forcard_errortypes. This is the issuer’s rejection reason and determines whether the fix is customer communication, rule adjustment, or integration change. - Check the Stripe Dashboard under Developers > Logs for the full request and response payload. The dashboard shows you exactly what your application sent and exactly what Stripe returned, which eliminates guesswork about whether the error is in your request or in Stripe’s response.
- Use Stripe’s test card numbers in your test environment to reproduce the specific error before deploying a fix. Stripe provides test cards for every major error scenario including specific decline codes, 3DS flows, and currency failures.
For subscription-based applications where payment errors directly affect recurring revenue, this guide on launching a subscription-based app without developers covers the full payment architecture in the context of no-code and AI-built products.
FAQ
What is the most common Stripe error for new SaaS products?
Card declines with a do_not_honor or generic decline code are the highest-volume Stripe error for new SaaS products, because customers’ banks flag first-time transactions with unfamiliar merchants as potentially suspicious. According to Stripe, this category of soft decline is retryable, and Stripe’s Smart Retries feature for subscription billing automatically retries at the optimal time based on machine learning models trained on payment recovery patterns across millions of transactions (Stripe, 2024). For one-time charges, surfacing a clear customer-facing message to try a different card or contact their bank recovers a meaningful share of these failed attempts.
How do I test Stripe payment errors without using real cards?
Stripe provides a full set of test card numbers that trigger specific error responses in test mode. The card 4000000000000002 always returns a card_declined error. The card 4000000000009995 returns insufficient_funds. The card 4000002500003155 triggers 3DS authentication. Using these test cards in your Stripe test environment before going live lets you confirm that your error handling, customer messaging, and retry logic work correctly before a real customer encounters a failed payment. All test cards use any future expiry date, any three-digit CVC, and any billing ZIP code.
Why is my Stripe webhook not firing in production when it works in development?
The most common reason is that your production webhook endpoint URL is not registered in the Stripe Dashboard, or that it is registered with an HTTP URL rather than HTTPS. Stripe requires HTTPS for all production webhook endpoints and will not deliver events to insecure URLs. The second most common reason is that the webhook signing secret in your production environment variables is the test mode secret rather than the live mode secret. Each mode in Stripe has its own signing secret, and using the test secret in production causes signature verification to fail on every incoming webhook, which your handler correctly rejects. This post on creative debugging for no-code builders covers the diagnostic approach for these types of environment-specific failures.
How do I prevent duplicate Stripe charges in a no-code or AI-built app?
Use idempotency keys on every Stripe API call that creates or modifies a resource. Generate a UUID when the customer initiates payment, store it with the pending order record, and pass it as the Idempotency-Key header with every API call for that transaction. If a network timeout causes your client to retry, the same key ensures Stripe returns the original response rather than processing a second charge. In imagine.bo-generated applications, include this requirement explicitly in your payment integration prompt or assign it as a specific task through the Hire a Human feature, since idempotency key management requires precise implementation to work correctly under all network conditions.
Do I need a developer to fix Stripe payment errors in an imagine.bo app?
Most Stripe configuration errors, including API key misconfigurations, currency settings, and customer-facing error messages, can be corrected through conversational prompts in imagine.bo’s Describe-to-Build interface. For webhook signature verification, 3DS authentication flows, idempotency key implementation, and regional payment compliance, using the Hire a Human feature is the recommended path. These are precision engineering tasks where approximate implementation creates silent failures rather than obvious errors. According to Stripe, webhook and authentication integration errors are the category most frequently linked to production revenue loss rather than test environment failures, precisely because they pass all basic tests but fail under real-world conditions (Stripe, 2024).
Conclusion
Three things to take away from this guide. First, every Stripe error has a specific type, code, and decline code that tells you exactly which category of problem you are dealing with. Reading all three before touching any code eliminates the most common debugging pattern of fixing the wrong thing. Second, webhook failures and authentication errors are the two error types most likely to cause silent revenue loss, because they do not surface to the customer and do not appear in payment dashboards unless you are logging errors explicitly. Third, idempotency keys and 3DS authentication support are not optional implementation details. They are baseline requirements for any production payment integration, and skipping either creates failure modes that are invisible in standard analytics.
For founders building payment-enabled applications on imagine.bo, the Pro plan at $25 per month includes access to Hire a Human with 20% off engineering tasks, which makes precise payment implementation affordable even at early revenue stages. Use the Describe-to-Build interface for standard payment setup and the Hire a Human feature specifically for webhook implementation, 3DS handling, and regional payment compliance. For a complete guide to building a SaaS application with payment processing using AI and no-code tools, this post on how to build a SaaS with AI and no-code covers the full architecture from first prompt to production payments.
Launch Your App Today
Ready to launch? Skip the tech stress. Describe, Build, Launch in three simple steps.
Build